When a victim is directed to a "secure" cryptocurrency trading platform or an offshore banking portal, the website they land on often looks absolutely flawless. The domain name might look highly professional, the SSL certificates are perfectly valid, and the website itself might even have years of established history and a completely clean reputation on Google search results.
For the victim, this creates an overwhelming sense of security. How could this "investment dashboard" be a scam if the website has been registered and active for half a decade? The devastating truth is that the scammers did not build this trusted digital real estate. They stole it.
At Trusted Private Investigators, our digital forensics team routinely tracks stolen cryptocurrency assets and unmasks anonymous harassers by following the digital breadcrumbs back to their source. The trail of a romance scammer frequently leading us directly into the compromised backend of hijacked small business websites.
Understanding the WordPress Backup Migration CVE-2023-6553 Vulnerability
To execute these stealthy server takeovers, scammers monitor public vulnerability databases like Exploit-DB. One of the most frequently abused entry points is a critical vulnerability known as CVE-2023-6553, found in the popular WordPress Backup Migration plugin (versions 1.3.7 and older).
Critical RCE Warning
CVE-2023-6553 is classified as an Unauthenticated Remote Command Execution (RCE) vulnerability. A threat actor does not need a password or username to take total control of the underlying server.
Small business owners naturally install backup plugins to protect their data, ironically providing the exact mechanism threat actors need to destroy it. Small businesses frequently use shared hosting solutions—such as Hostinger or InterServer—and often neglect essential maintenance, leaving these outdated plugins active.
The Technical Mechanics of the Server Hijack
In the case of this Backup Migration exploit, the attackers target a specific, vulnerable file within the plugin’s architecture called backup-heart.php. The scammers manipulate an HTTP request header known as Content-Dir.
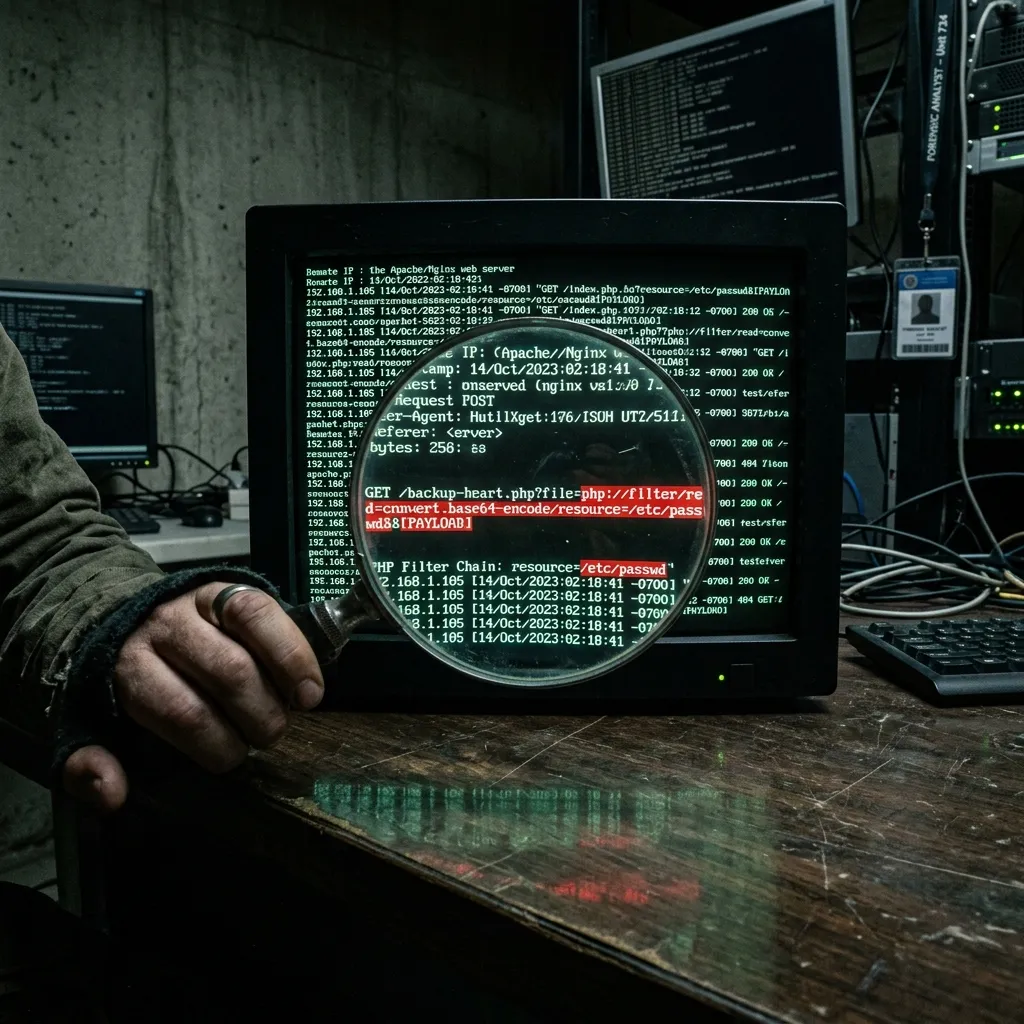
By utilizing an evasion technique known as "PHP Filter Chaining," the attacker can force the server's backend to execute malicious code without triggering firewall alerts. This trickery compiles a malicious payload directly in memory. From that moment on, they have a backdoor, allowing them to host fake investment fraud portals on a domain with a pristine reputation.
How Threat Actors Use Anti-Detect Browsers to Hide
Managing dozens of hijacked websites across multiple victims requires a staggering level of operational security (OPSEC). To avoid detection, sophisticated scam syndicates use specialized anti-detect browsers such as GoLogin, AdsPower, Undetectable.io, and MoreLogin.

- Hardware Spoofing: Spoofing OS, graphics card metadata, and screen resolution.
- Geolocation Spoofing: Integrating proxy networks to match the "backstory" told to the victim.
- Session Isolation: Completely isolating cookies and cache for every individual "browser profile."
The Professional Digital Forensics Process for Tracing Scammers
Despite the use of proxies and anti-detect tools, digital actions leave digital reactions. Our team uses a multi-phased server-side deconstruction to unmask perpetrators:
- Log Analysis: Mapping the exploitation vector used (e.g., PHP filter chains on
backup-heart.php). - CDN Bypassing: Identifying the true origin IP hidden behind Cloudflare via historical DNS and SSL parsing.
- Proxy Piercing: Deploying legally compliant, active digital attribution tracking links to force leaks of the operator's real IP.
- Blockchain Tracing: Using enterprise analytics to follow stolen funds until they land at a centralized exchange like Binance.
The Legal and Financial Risks of Hiring a Hacker
Never Hire "Hackers for Hire"
Desperate victims often turn to anonymous "hackers" to recover funds. This is a common door for "recovery scammers" who will lead to further loss.
Even if genuine, "hacker" methods often destroy the case. Aggressive scanning triggers the scammer's monitoring, causing them to "burn the server"—deleting evidence and vanishing. Furthermore, illegally obtained evidence is inadmissible in court, and you may face civil liability for unauthorized cyberattacks.
Stop Guessing and Start a Professional Investigation
Digital footprints cannot be completely erased. If you suspect a loved one is being directed toward a fraudulent portal, time is the critical factor. Do not confront the scammer. Secure the links, document all chat logs, and engage a licensed investigative team.
