Infidelity in the digital age often involves the theft of cryptocurrency assets during the dissolution of a partnership or via a sophisticated phishing attack. The Tron network has become a preferred channel for these illicit movements due to its low fees and high throughput. When you see your Tether (USDT) move from your wallet to an unknown address, the feeling of helplessness is overwhelming. But the Tron blockchain is a public ledger, and every movement of a TRC20 token is a permanent record. The attacker relies on your lack of technical knowledge to hide their tracks, but the data is there for those who know how to extract it.
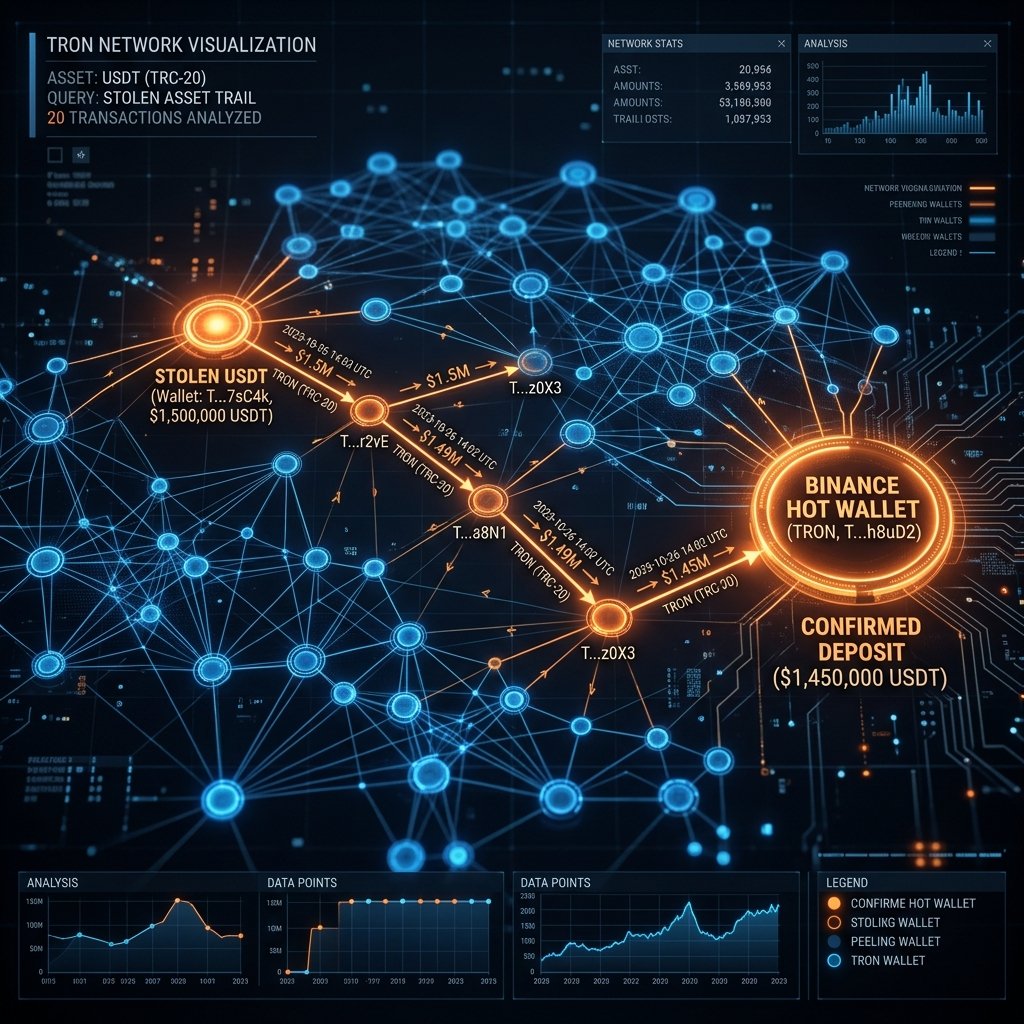
If you are determined to trace stolen USDT on Tron network to Binance, you are engaging in a process of forensic pathfinding. You must follow the "hops" across multiple wallets until the assets land in a cluster that can be linked to a physical identity. One of the most powerful tools for visualizing these clusters and mapping the flow of stolen Tether is GraphSense. Below, we detail the technical deployment of this engine and the massive infrastructure requirements that drive victims toward professional services.
GraphSense: The Professional Analytics Engine for Crypto Forensics
GraphSense is a high performance crypto asset analytics dashboard designed for institutional grade investigations. Unlike a simple block explorer that only shows one transaction at a time, GraphSense allows an investigator to see the "Graphic Representation" of the entire network. It categorizes wallet clusters, identifies known exchanges, and maps the relationships between distinct addresses. In the world of Tron forensics, this is the only way to see through the "Peel Chain" tactics used by criminals to obfuscate the origin of funds.
The core utility of GraphSense lies in its ability to handle "Multi Chain Forensic Mapping." It allows you to follow the assets even if the attacker attempts to use a "Bridge" to move from the Tron network to another chain. By identifying the "Inflow" and "Outflow" patterns, researchers can pinpoint the exact moment the stolen USDT enters a centralized environment the cluster of addresses used by major exchanges like Binance to process user deposits.
Operational Deployment Configuration and Analytics Logic
To deploy GraphSense effectively, an investigator must host a specialized server environment. Experts use Linux typically a high performance distribution like Debian or Cent OS to manage the complex data processing pipelines required to index the Tron network. The tool is modular, meaning you must configure a backend database (typically Cassandra) to store the indexed blockchain data before you can run your first query.
1. Environment Configuration: The server must have Docker and Python installed to manage the different microservices of the GraphSense stack. The architecture is designed for parallel processing, and it requires a multi core CPU to handle the transactional volume of the Tron blockchain.
2. Source Acquisition: Source the tool directly from the official repository to ensure the latest network signatures for the Tron TRC20 protocol.
- Official Tool Link: GraphSense Dashboard on GitHub
3. Technical Execution: Once the environment is containerized and the data pipeline is active, the investigation process involves these steps:
# Initialize the GraphSense environment via Docker
docker-compose up -d
# Trigger the indexing of the Tron network logs
python3 graphsense-ingest.py --network tron
# Perform a cluster analysis on the target wallet
graphsense-cli search [stolen_wallet_hash]When the analysis executes, the engine begins mapping the movement of the stolen Tether. It identifies every wallet that has received a portion of the funds and flags any that match the signature of a Binance Hot Wallet. This "Exchange Attribution" is what allows for a legal intervention.
Mapping the Transaction Hops and Identifying the Binance Destination
The movement of stolen USDT is rarely a straight line. Attackers perform a "Peel Chain," sending the total amount to a new wallet, then sending 90% to another, and 10% to a final destination. This is designed to confuse simple trackers. GraphSense allows you to see through this by visualizing the "Full Tree" of transactions. You watch the balance move across five or six distinct hops until it finally hits a "Deposit Cluster." If that cluster is identified as part of the Binance ecosystem, you have found the point where the attacker's anonymity ends.
The Full Node Sync Wall of Friction: A Hardware Barrier
While GraphSense is a definitive tool, it presents a massive "Wall of Friction" that stops almost every DIY investigator. The tool does not work in a vacuum; it requires a Full Tron Blockchain Node. To query the data in real time, you must download and verify every single block that has ever existed on the Tron network. This is not a "plug and play" solution; it is an industrial data engineering project.

For a victim of a theft, this "Synchronization Delay" is the greatest obstacle to recovery. While your node is spending two weeks "Syncing" with the network, the attacker has already moved the USDT to Binance, converted it to XMR or fiat, and vanished. By the time your dashboard is ready to run a query, the funds are long gone. A DIY investigation is a race against a clock that you don't even have access to yet.
The Terabyte Storage and Performance Bottleneck
The hardware requirements for hosting a Tron full node are staggering. You need a dedicated server with terabytes of high speed storage and significant RAM capacity to handle the indexing of the TRC20 logs. Consumer grade external hard drives are insufficient for this task; you need enterprise grade NVMe SSDs to maintain the I/O throughput. Spending thousands of dollars on hardware and waiting weeks for a sync is a "Resource Drain" that most victims cannot afford while their life savings are in transit.
Professional Attribution Pivot and Rapid Asset Freezing
At Trusted Private Investigators, we do not wait for node syncs or hardware cycles. We operate on pre indexed, institutional grade data pipelines that allow us to achieve total attribution in a fraction of the time required by amateur methods.
Achieving Total Attribution in 10 Minutes
Our team utilizes enterprise licenses for Chainalysis and TRM Labs, the same platforms used by global law enforcement agencies. We do not have to index the Tron network manually; we enter the transaction hash and see the full cluster map in under 10 minutes. We identify the Binance deposit wallet and the associated user identity before the attacker has a chance to off ramp. We move at the speed of the blockchain, not the speed of an SSD.
Drafting the Institutional Subpoena and Legal Hold
Once the Binance destination is confirmed, we act immediately. We produce the Forensic Attribution Report and the necessary legal documents to initiate a hold on the attacker's account. We provide the "Direct Flow Evidence" that proves the assets in that specific Binance account are the result of the initial theft. We don't just follow the trail; we secure the destination.
The Enterprise Pivot: Reclaim Your Assets with TrustedPI
The Tron network is designed for speed, and criminals exploit that speed to outrun their victims. A "DIY search" with open source tools is a noble attempt, but it is often a race that is lost before it begins. You are fighting against hardware limitations, synchronization delays, and the technical obfuscation tactics of a professional predator. You need a solution that is already in place and ready to strike.
The difference between a "GraphSense query" and a "Professional Investigation" is the Finality of the Result. One gives you a technical chart; the other gives you a legal freeze and a path to recovery. If you have been a victim of a USDT theft on the Tron network, do not let the trail go cold. You deserve professional protection and undeniable proof.