Romance scams are arguably the most insidious form of digital theft. They do not rely on zero-day exploits or complex smart contract vulnerabilities, they exploit human loneliness.
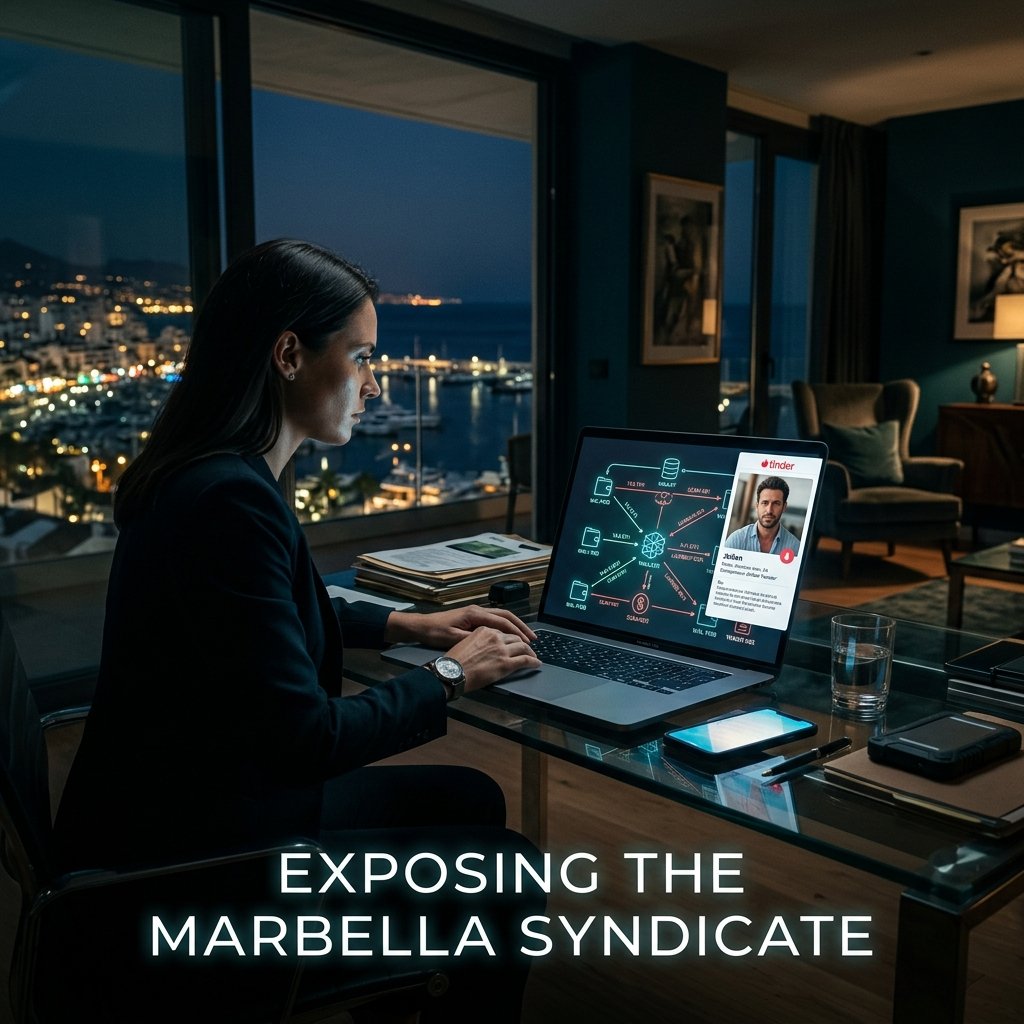
Over the past few months, my team and I have been tracking a sophisticated syndicate operating out of Spain, specifically targeting elderly and widowed individuals on dating apps. Today, I am going to break down exactly how we traced $358,210 in stolen USDT, mapped the syndicate’s on-chain laundering infrastructure, uncovered their fatal operational security failures, and successfully recovered the funds for a 72-year-old victim.
Case File
#TR-2025-884
Target Location
Marbella, Spain
Target Assets
USDT (ERC-20)
Anatomy of the Tinder Syndicate
In early January, I was contacted by the family of "Martha," a 72-year-old widow. Martha had matched with "Antonio," a supposedly wealthy architect living between Miami and Spain. The grooming phase lasted three months. Antonio built immense trust, eventually convincing Martha to invest her retirement savings into a "guaranteed high-yield crypto node."
Between February 12th and March 5th, Martha was walked through the process of buying USDT on Coinbase and transferring it to a decentralized wallet controlled by the scammer.
Investigation Subject: Wallet Chain
- Victim Wallet: 0x4A9e91...88c2
- Scammer Initial (Wallet A): 0x8F2d1B...3d9A
Technical Deep Dive: Mapping Cross-Chain Transfers
To trace the funds across the bridge, we utilize the Web3.py library to automate the detection of outgoing bridge transactions and correlate them with incoming transactions on the destination chain.
import requests
from web3 import Web3
import time
#, FORENSIC PARAMETERS, ETHERSCAN_API_KEY = 'YOUR_KEY'
SCAMMER_WALLET = '0x8F2d1B...'
ACROSS_BRIDGE_ADDRESS = '0x4D9079Bb4165aeb4084c526a32695dCfd2F77381'
def get_transactions(address):
url = f"https://api.etherscan.io/api?module=account&action=tokentx&address={address}&sort=asc&apikey={ETHERSCAN_API_KEY}"
return requests.get(url).json().get('result', [])
print(f"[*] Scanning transactions for {SCAMMER_WALLET}...")
txs = get_transactions(SCAMMER_WALLET)
for tx in txs:
if tx['to'].lower() == ACROSS_BRIDGE_ADDRESS.lower():
print(f"[!] Bridge Transfer Detected!")
print(f" TxHash: {tx['hash']}")
print(f" Amount: {Web3.from_wei(int(tx['value']), 'ether')} ETH")
By correlating the exact timestamp and amount sent to the bridge on Ethereum with the Arbitrum ledger, we identified the receiving wallet: 0xC3a19...77b1.
The Fatal OpSec Flaw
Even with advanced anti-detect environments and specialized multi-account browsers, human error is the ultimate vulnerability. The scammer needed to pay for server hosting for their next victim's fake exchange. They used a small amount of stolen ETH to pay for the hosting service, linking their stolen funds to a commercial VPN subscription they had paid for three months earlier using the same intermediary wallet.
Legal preservation requests issued to the VPN provider yielded a registration email: marbella.architect88@protonmail.com.
Technical Deep Dive: De-Anonymizing the Identity
Having an email is the pivot point. We deploy digital reconnaissance tools like Sherlock and Holehe to search thousands of social networks and find registered accounts linked to the target's handle.
$ python3 sherlock marbella.architect88 --timeout 5 [+] Instagram: https://instagram.com/marbella.architect88 [+] Pinterest: https://pinterest.com/marbella.architect88 [+] Spotify: https://open.spotify.com/user/marbella.architect88 $ holehe marbella.architect88@protonmail.com [+] Instagram: Registered [+] Airbnb: Registered
The Instagram account led us to a real name associated with a luxury car rental service in Marbella: Alejandro V.
Following the Fiat Cash-Out
Confident in his obfuscation, Alejandro moved the remaining funds directly into a deposit address at Kraken, a centralized, KYC-compliant exchange. This is the holy grail for an investigator. Centralized exchanges require government IDs and facial scans.
- Destination: 0x99B2...KrakenDeposit
- TxHash: 0x77d8a9f...b2e41
Legal Freeze & Takedown
Recovery requires a strict legal protocol. We compiled a comprehensive "Source of Funds" report, combining Martha's KYC, police reports from the IC3, and an immutable transaction graph showing the flow of stolen wealth.
Emergency Injunction
Worked with legal counsel to file injunctive relief, providing irrefutable on-chain proof to Kraken's Law Enforcement portal.
Global Freeze
The exchange compliance team flagged the account, preventing Alejandro from withdrawing the cash to his Spanish bank account.
Interpol/UDEF Strike
Spanish authorities (UDEF) raided a luxury villa in Marbella, arresting Alejandro V. and recovering devices used for the Tinder profiles.
Conclusion
As of yesterday, $358,210 is safely back in the hands of its rightful owner. The blockchain is a double-edged sword. Scammers use its speed, but investigators use its permanence. We only need to be right once, the scammer has to be perfect forever.