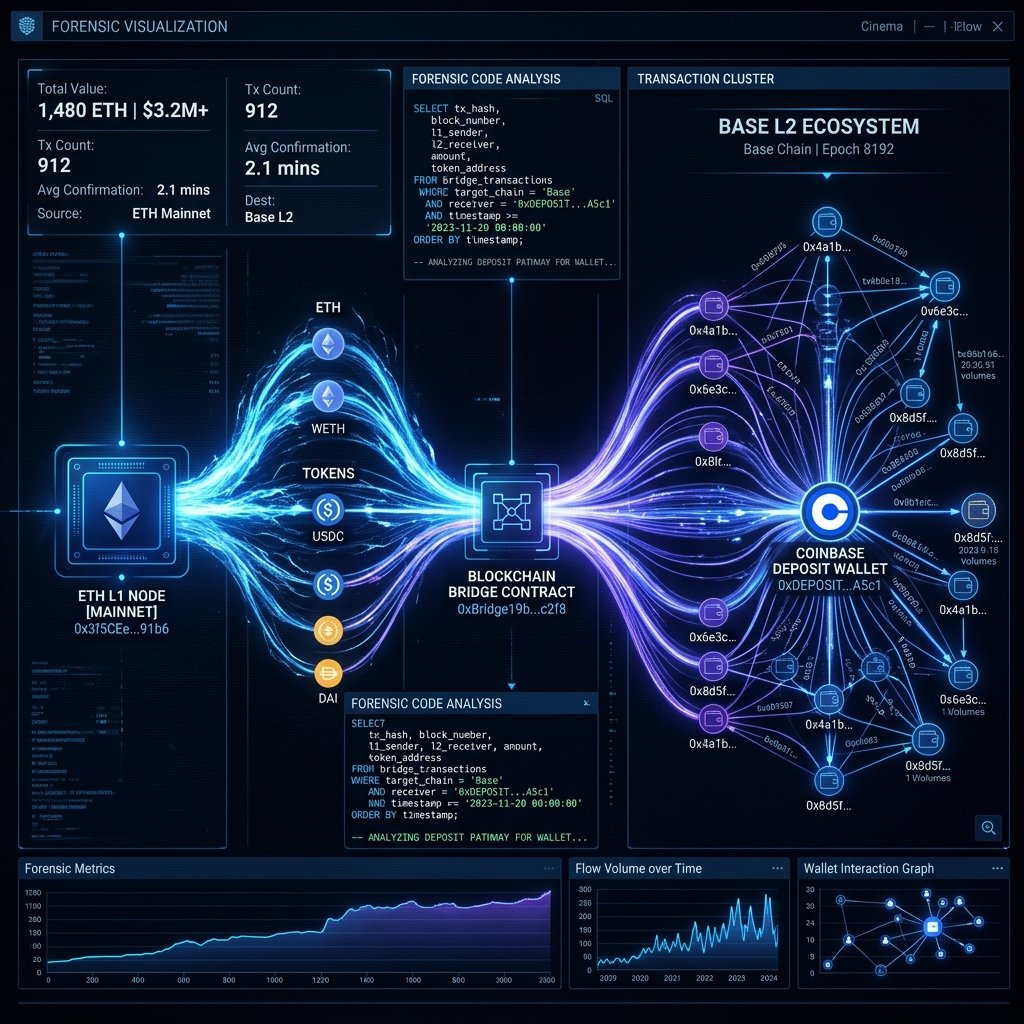
The rise of Layer 2 (L2) networks like Base has revolutionized blockchain scalability, but it has also provided a new playground for digital predators. When a scammer drains a wallet on the Ethereum mainnet, their primary objective is to move those funds to a controlled environment where they can be "washed" or off ramped. One of the most common maneuvers involves using the official Base Bridge to move stolen ETH or USDC onto the Base network. To the average victim, this looks like the money has "vanished" into a different dimension. But an L2 bridge is not a black hole; it is a smart contract that emits definitive events for every deposit and withdrawal.
To trace stolen funds bridged to Base network sent to Coinbase, you must move beyond simple block explorers. You need a way to correlate transaction events on the Ethereum Layer 1 (L1) with the resulting mint events on the Base Layer 2. This requires a professional understanding of "Relayer Semantics" and the ability to query massive datasets in real time. One of the most accessible tools for this high resolution tracing is Dune Analytics. Below, we detail the technical SQL architecture required for bridge monitoring and the systemic failures of public tools.
Dune Analytics: The Open SQL Engine for Multi Chain Forensics
Dune Analytics is a high performance blockchain data platform that allows researchers to write custom SQL queries against the raw transaction logs of multiple networks. Unlike a standard search tool, Dune allows you to join data from different chains within a single dashboard. For an investigator, this is critical because it allows for the "Cross Chain Pivot" the ability to see a deposit on L1 and find its corresponding credit on L2 without manual searching.
The core power of Dune lies in its abstraction of the "Bridge Messaging Layer." When assets move across the Base bridge, a message is sent from L1 to L2. By querying the `base.bridge` tables, an investigator can identify the "Sequencer" transactions that represent the attacker's funds reaching the destination. This provides the first verified link in the chain of custody after the bridge interaction occurs.
Technical Tutorial: Writing the L1 to L2 Bridge Monitor Query
To monitor the bridge effectively, an investigator must write a custom SQL script that filters for "Bridge Initiated" events. This requires identifying the specific contract address of the Base Standard Bridge on the Ethereum mainnet. The objective is to isolate every transaction where your stolen wallet address appears as the "Initiator" of a bridge request.
1. Environment Configuration: Create a new query in the Dune dashboard (V2 Engine). You must utilize the Spark SQL syntax to handle the complex joins required for cross chain attribution.
2. Source Specification: You must query the `base.deposits` table, which tracks every asset that enters the network via the official bridge relayers.
- Official Tool Link: Dune Analytics Framework on GitHub
3. Technical SQL Execution: The following query logic is used to isolate an attacker's movement through the bridge:
-- Monitor the Base Bridge for specific wallet interactions
SELECT
block_time,
tx_hash,
from_address as attacker_l1_wallet,
to_address as l2_destination,
value / 1e18 as eth_amount
FROM base.deposits
WHERE from_address = [your_stolen_wallet_address]
ORDER BY block_time DESC
LIMIT 10When this query executes, the engine scans the bridge logs. It returns the exact L2 transaction hash that represents the attacker receiving the funds on the Base network. From here, you can pivot your investigation to the Base network logs to find where those funds were sent next typically a deposit address at a major exchange like Coinbase.
Identifying the Attacker L2 Hash and Coinbase Destination
Once you have the L2 hash, the hunt accelerates. You must follow the funds as they move across the Base network. Attackers rarely keep funds in their "Bridge Receiving" wallet for more than a few minutes. They will perform a "Fan Out" maneuver, spliting the funds into smaller amounts, or send them directly to a centralized "Off Ramp." By running a secondary query on the `base.transactions` table, you can identify the final wallet cluster. If that cluster belongs to a known Coinbase Hot Wallet, you have found the point of legal interception.
The Community Tier Wall of Friction: A Latency Trap
While Dune Analytics is technically capable, the "Community Tier" used by most DIY investigators presents a severe Wall of Friction. The free version of the platform is designed for historical research, not active forensic response. When you are trying to catch a thief, every second counts, but a free Dune query can take minutes or even hours to enter the execution queue. This delay is the predator's greatest ally.
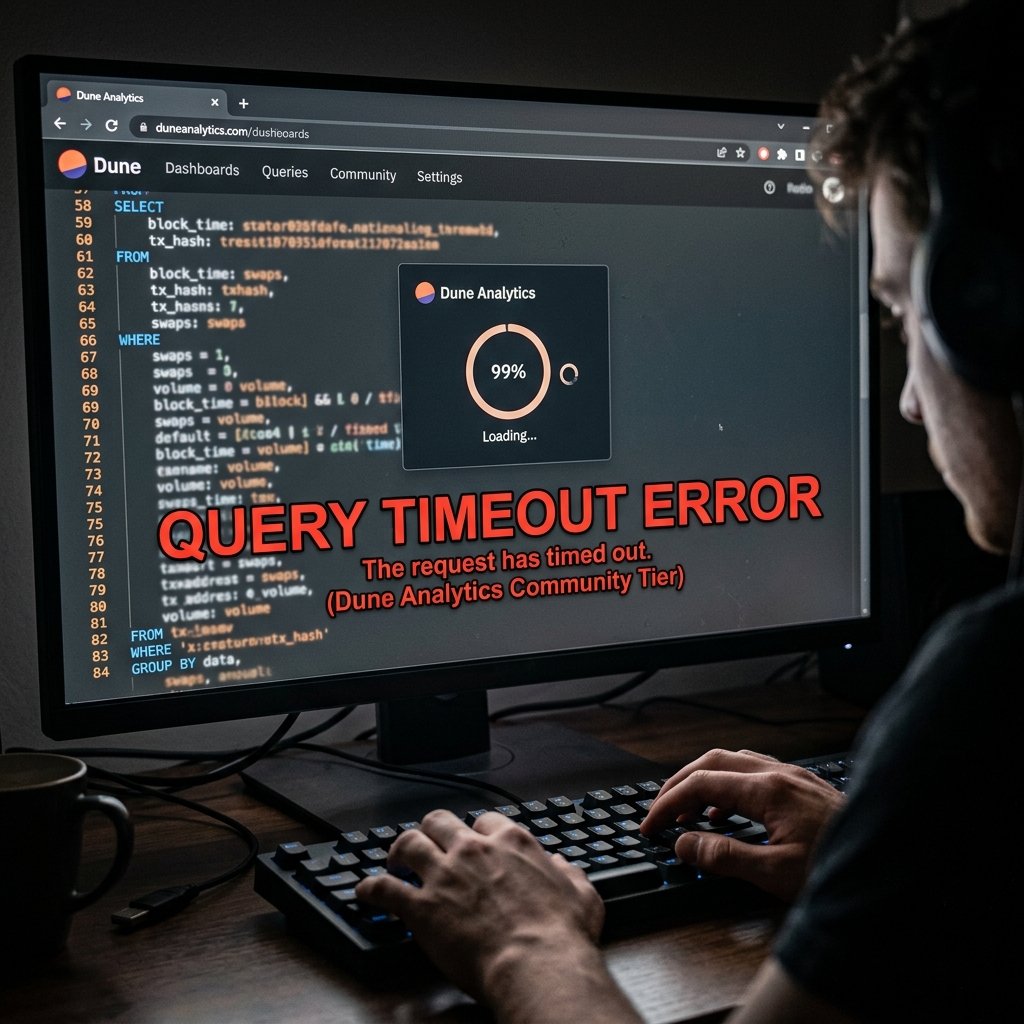
Furthermore, the community tier lacks access to the Real Time Mempool. You can only query data that has already been confirmed and indexed a process that has a natural delay of several blocks. If the attacker is moving funds quickly, they will have already deposited to Coinbase and initiated a withdrawal to a cold wallet or a mixer before your query even finishes its first scan. A DIY investigation is always one step behind the crime.
The Query Timeout Execution Barrier
Complex bridge traces involve joining data across multiple chains and millions of rows of transaction logs. On the public tier, these intensive queries often hit a "Time Limit" and are automatically terminated by the server to protect platform performance. You will see a red "Query Timeout" error just when you were about to find the link to the exchange. Trying to optimize these queries without advanced database management skills is a frustrating dead end that wastes the most valuable resource you have: Time.
Professional API Level Attribution and Tactical Recovery
At Trusted Private Investigators, we do not wait in query queues. We operate at the "Infrastructure Layer" of the blockchain. We utilize Live API Level Access to Base Network Indexers and enterprise licenses for TRM Labs, allowing us to achieve total attribution in seconds.
Tracking the Bridge Cross in Real Time
Our investigators use real time monitoring scripts that alert us the moment a target wallet interacts with the Base Bridge contract. We do not have to "query" the data after the fact; we are watching the mempool as the transaction is being verified. We identify the Coinbase deposit address as the funds cross the bridge, often before the attacker has even seen the confirmation on their own screen.
Emergency Asset Preservation and Global Subpoena Drafting
Speed is the only way to beat a bridge hop. As soon as the funds hit the Coinbase cluster, we initiate the Emergency Preservation Protocol. We draft the forensic attribution report and the legal preservation request, serving it to the exchange's legal department immediately. We provide the "Direct Bridge Correlation" that proves the funds on Base are the same assets stolen on Ethereum L1. We force the attacker's hand before they can disappear.
The Enterprise Pivot: Beat the Bridge with TrustedPI
Layer 2 networks are built for speed, and criminals take advantage of that speed to outrun their victims. A "DIY SQL" approach is a valiant effort, but it is like trying to catch a jet engine with a bicycle. You are fighting against platform latency, hardware timeouts, and a total lack of real time visibility. You need a team that has the API level dominance to see through the bridge shadow.
The difference between a "Dune query" and a "Professional Investigation" is the Rate of Attribution. One gives you a historical record; the other gives you a legal freeze. If you have lost assets to a bridge drainer, do not fight the "Wall of Friction" alone. You deserve professional protection and undeniable proof.