Imagine waking up, pouring a cup of coffee, and finding a standard, mundane email sitting in your inbox: "Password Reset Request." You didn't request a password reset. Most people in this situation assume it was a system glitch or that someone typed their username incorrectly. Annoyed, you click the link provided in the email to report the error or cancel the request.
In that single, fleeting moment, you haven't secured your account. You have just handed the keys to your entire digital life directly to a cybercriminal.
Within minutes, your actual password is changed. You are locked out of your banking portals, your cryptocurrency exchanges, your private communications, and your corporate infrastructure. If this is a targeted attack by a corporate spy or a deeply entrenched matrimonial adversary, the attacker will immediately begin deleting crucial evidence and initiating catastrophic data wipes to cover their tracks.
What is Host Header Password Reset Poisoning?
As a Certified Fraud Examiner and digital forensic investigator, I see this nightmare scenario every week. The technique they use isn't magic, and it doesn't require them to guess your complex password. It relies on a devastating manipulation of server trust known as Host Header Poisoning.
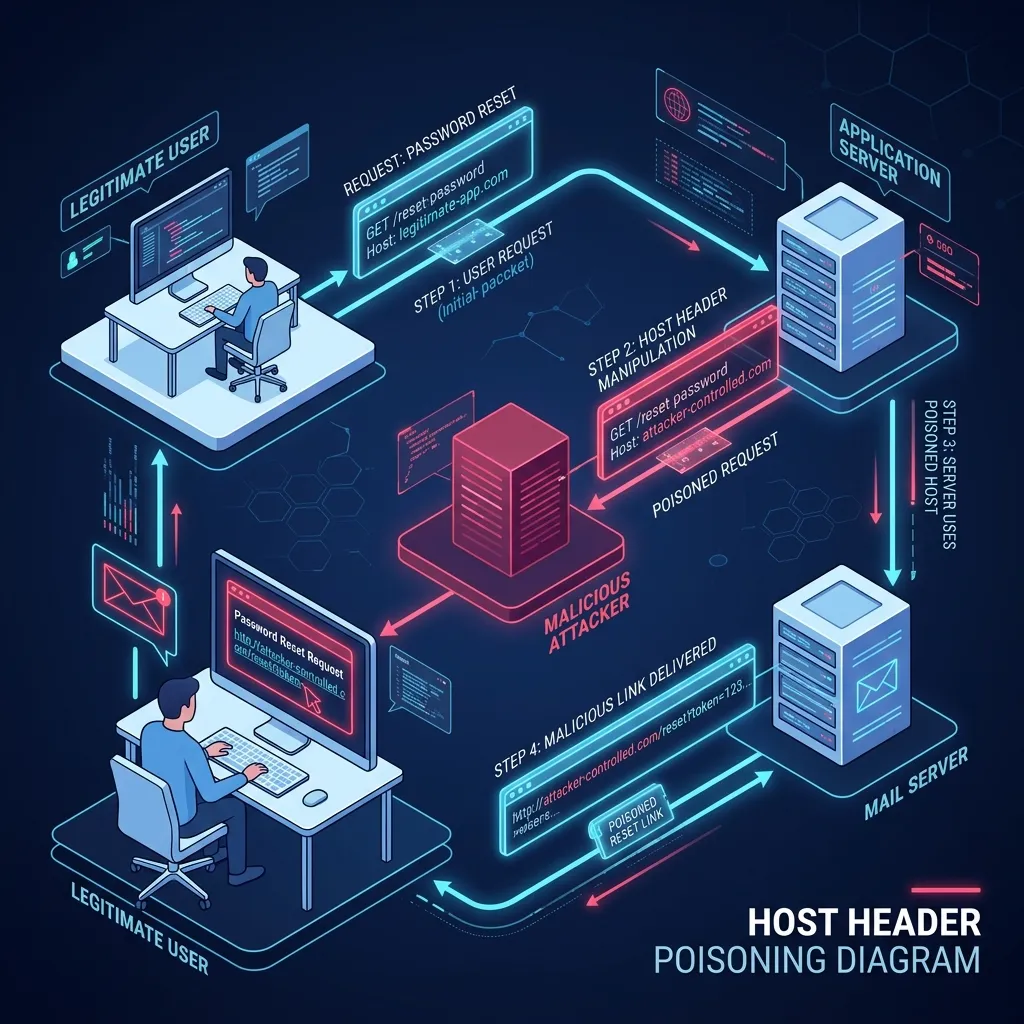
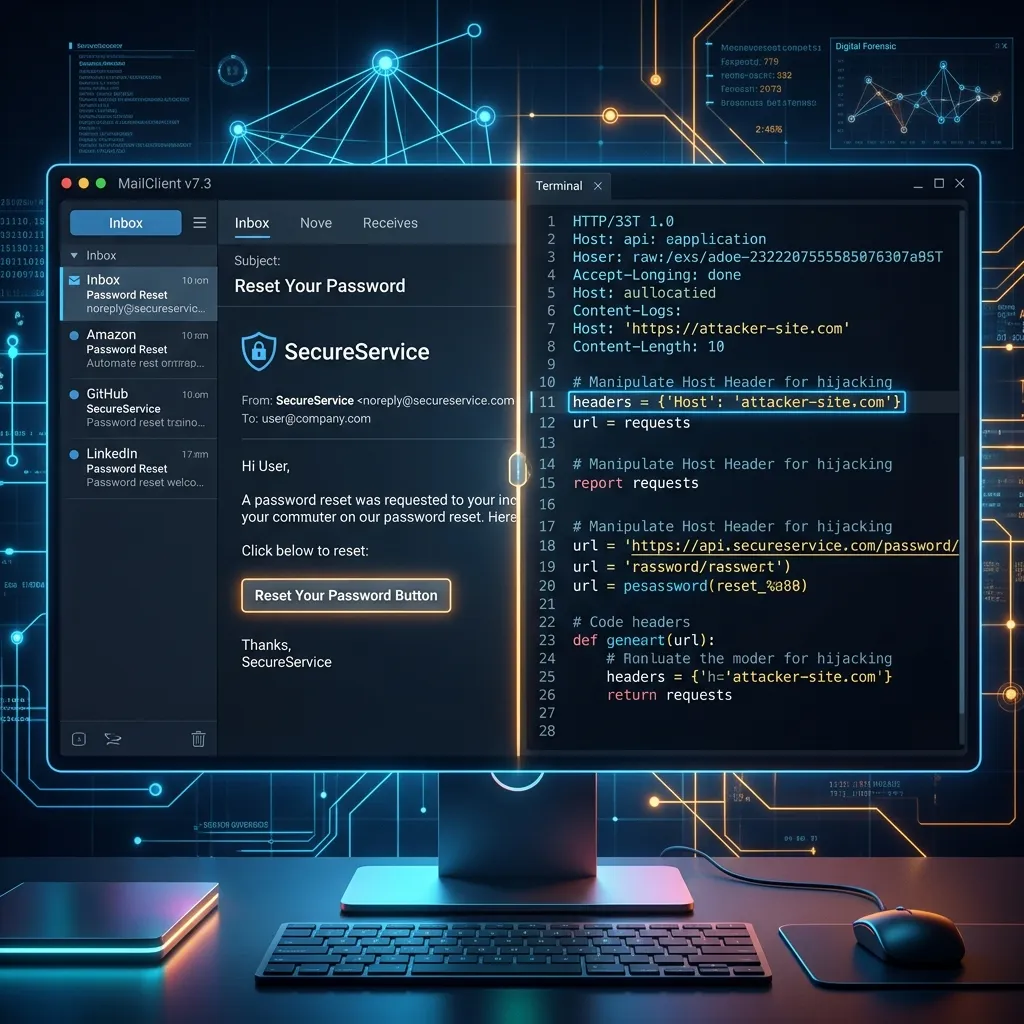
When you click "Forgot Password" on a website, the server generates a unique, secret cryptographic token and emails a reset link to the user on file. The server builds this link dynamically. It looks at the HTTP "Host" header in the web request to know which domain name to attach to the front of the token.
The Vulnerability: CVE-2025-25198
Many small-to-medium businesses, legal firms, and private individuals use self-hosted mail solutions to maintain privacy. A prime example is Mailcow, a highly popular, open-source mail server suite. While generally secure, it is vulnerable to highly specific architectural flaws if not strictly patched.
A critical vulnerability currently being weaponized in the wild is **CVE-2025-25198**, found
in Mailcow versions prior to 2025-01a. An attacker exploiting this flaw intentionally
manipulates the backend HTTP request, swapping out the legitimate "Host" header for a
malicious domain they control (e.g., attacker-controlled-server.com).
The Anatomy of an Email Account Takeover
The moment a victim clicks the "cancel" or "report" link in the poisoned email, their web browser navigates to the attacker's server, carrying the secret token in the URL. The attacker's server acts as a listener, instantly capturing the token parameter.
Administrative Lockout
The attacker now possesses the valid, server-generated cryptographic key. They immediately submit it to the legitimate server, lock the victim out, and gain total control.
They will download archives, forward incriminating communications to burner accounts, and then systematically purge the inbox. In severe cases, they may deploy "wiper" malware—malicious code designed to permanently overwrite hard drives and destroy the server's operating system.
How Digital Forensics Recovers Data After a Wiper Attack
As an EnCase Certified Examiner (EnCE), I have built my career on a singular truth: Data is remarkably resilient. Deleting a file or deploying a wiper virus rarely eradicates the data completely; it merely severs the operating system's logical path to that data.

Hex-Level Drive Carving
When a client contacts us following a wipe, we image the physical server drives at the bit-level. Even if the file allocation tables (FAT/MFT) are destroyed, the raw 1s and 0s still exist. We look for distinct hexadecimal signatures of SQLite databases and Maildir text blocks to piece together fragmented emails.
Network Artifact and Reverse IP Tracing
While the attacker may have wiped local logs, they cannot wipe the global internet infrastructure. To execute the attack, the attacker forced the victim to click a link pointing to an external domain. We extract that exact domain and use historical DNS analysis and OSINT to strip away their proxy protections, tracing SSL certificates and registration data back to the source.
Reclaim Your Digital Life Today
Cybercriminals rely on your panic and their perceived technological superiority. They under-estimate the science of digital forensics. If your corporate servers have been maliciously wiped or you suspect a compromise, do not attempt to "fix" the server yourself.