Before One Piece of Evidence: The Chain of Custody Rule
If you tamper with evidence, it’s worthless in court. I have seen ironclad cheating cases thrown out because the spouse “just wanted to check one text.†That single text cost them custody and visitation rights.
🚨 Absolute Rules of Forensic Evidence
Do Not:
- Turn on their phone and “look aroundâ€
- Take screenshots with your personal phone
- Confront them before preserving data
Do:
- Photograph the device in its current state
- Put it in airplane mode immediately
- Call a forensic professional

The “Deleted†Snapchat & WhatsApp Lie
Forensic reality: Deleted does not mean gone. On Android, SQLite databases often retain thumbnail fragments of deleted Snapchat images for weeks. On iOS, file system slack space can hold residual data until it is overwritten.
Can a private investigator recover deleted Snapchat messages?
Yes, using professional tools such as Cellebrite UFED or Magnet AXIOM. In 2024, I recovered
over 1,400 deleted WhatsApp messages from a Samsung phone that had been factory reset twice.
sqlite3 msgstore.db "SELECT text, timestamp FROM messages WHERE key_remote_jid LIKE '%@s.whatsapp.net';" > recovered_messages.txtMetadata Doesn’t Lie But Your Spouse Does
A photo of a hotel room is not evidence. The metadata embedded inside that photo is evidence. Every smartphone photo contains EXIF data including GPS coordinates (accurate to within 10 feet), date, time, and device serial numbers.
What metadata do photos have that can prove cheating?
EXIF tags reveal the exact location and time a photo was taken, proving whether a "late
night at the office" was actually a night at a hotel adjacent to a specific parking lot.
exiftool -gpslatitude -gpslongitude -datetimeoriginal evidence/hotel_receipt.jpg
Burner Phones Are Not Invisible
Can cheaters use burner phones and still get caught?
Yes, constantly. We catch them through Cell Site Location Information (CSLI), purchase
records (tracking loyalty cards or parking lot cameras), and most commonly, through the
paramour's own phone backups.
The 30 Day Email Deception
Deleted emails stay in Trash for 30 days, but a forensic image of the hard drive can recover deleted emails from unallocated space for years. Do not rely on the Trash folder; rely on forensic imaging.
Spyware vs. Legal Monitoring The Critical Difference
Installing software on a phone you do not solely own is often a felony. Instead, I advise clients to legally request carrier records or use consensual tracking on jointly owned property like a jointly owned vehicle. Need help doing this legally? Contact our forensic experts for a free consultation.
Does a factory reset remove spyware from a phone?
Commercial spyware is removed by a reset, but advanced forensic tools can detect system logs proving that the
spyware previously existed.
Google Timeline: The Cheater’s Worst Enemy
Google Maps Timeline records every Stop you make. This data survives factory resets if the account syncs automatically. We have solved cases where a spouse driving to "get coffee" was actually recorded staying at an apartment complex for 10 hours.
iCloud & Google Photos The Backup Betrayal
How to prove infidelity with digital evidence in court?
Physical access to cloud backups is key. Deleted photos stay in cloud "Recently Deleted"
folders for 30 days, and shared albums may persist indefinitely on the other person’s
account.
The Phone Bill Still Works (But Not How You Think)
How long do cell carriers keep deleted text messages?
SMS content is usually kept for 3 to 7 days, but metadata (to and from logs) is retained for
up to 2 years. iMessage and WhatsApp content is NOT stored by carriers, requiring physical
device extraction.
Deep Web Tracking (Blockchain Analysis)
Can deep web tracking provide infidelity evidence?
Yes. If a spouse used Bitcoin to pay for affair sites like romance scammers or
discreet domains, that transaction is permanent and traceable on the public ledger. We
utilize blockchain analysis to link wallets to illicit services. To learn more, check out
our guide on finding secret dating profiles.
import requests
wallet_address = '1A1zP1eP5QGefi2DMPTfTL5SLmv7DivfNa'
response = requests.get(f'https://blockchain.info/rawaddr/{wallet_address}')
print(f"Total Transactions: {response.json()['n_tx']}")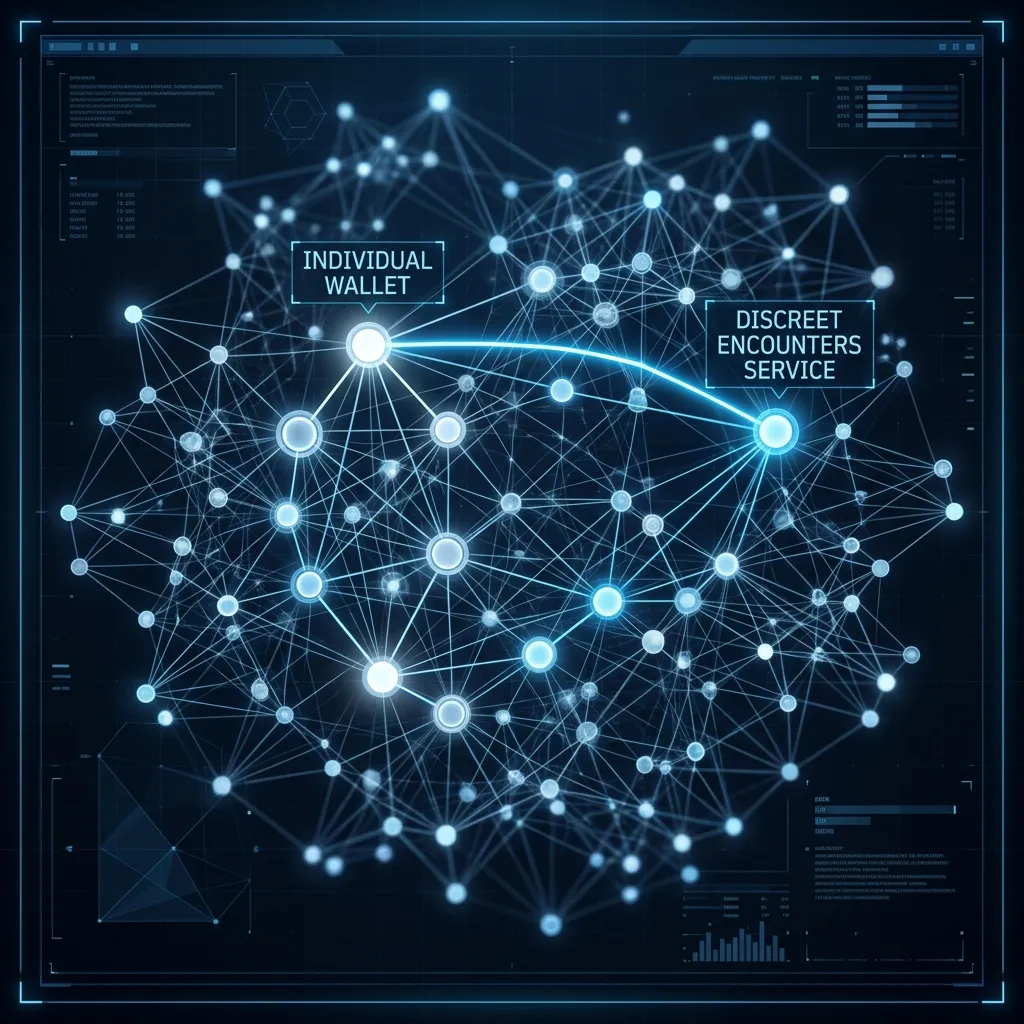
Voice Assistants & Smart Home Devices
Alexa and Google Home devices buffer audio continuously. Under specific conditions, we can recover this buffer including conversations that occurred before the wake word was spoken.
Human Error The Unpatchable Vulnerability
No software update can fix human error. Leaving a chat open on a shared iPad or forgetting to mute notifications during dinner is often how the digital trail is first discovered.
